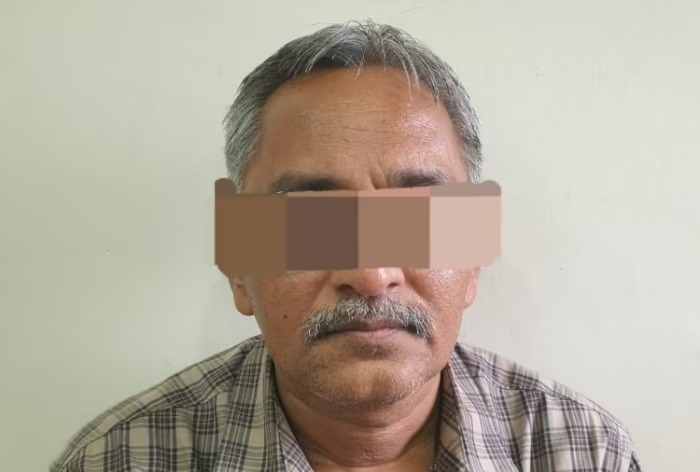
On October 20, the Anti-Terrorist Squad (ATS) of the Gujarat Police apprehended a 53-year-old man. He had immigrated from Pakistan in early 1999 and was subsequently granted Indian citizenship in 2005. The arrest was made on charges of allegedly spying for Islamabad. It is alleged that he infected the phones of Indian defence personnel with malware distributed via WhatsApp.
The accused, identified as Labhshankar Duryodhan Maheshwari was arrested on charges of aiding Pakistani agents in obtaining sensitive information about Indian soldiers. Originally hailing from Pakistan, Maheshwari was allegedly engaged in espionage activities on behalf of Islamabad. According to police officials, he was distributing malware through WhatsApp to compromise the phones of Indian defence personnel.
Reportedly, Maheshwari, a native of Pakistan, arrived in Gujarat’s Tarapur town in the Anand district in 1999 along with his wife for fertility treatment. Despite the initial purpose of his visit, he chose to remain in India and went on to establish a prosperous business. In 2005, he was granted Indian citizenship, but his extended family continued to reside in Pakistan.
ATS superintendent of police, Om Prakash Jat, stated, “Labhshankar Maheshwari, who was living in Tarapur town of Anand district, has been arrested on accusations that he circulated malware through WhatsApp among defence personnel, which was used by Pakistani intelligence agencies to obtain information from their phones.”
ATS Superintendent of Police, Jat, further stated that Maheshwari has been charged under Indian Penal Code (IPC) Section 123, which pertains to concealing with the intent to facilitate a design to wage war against the government, as well as Section 121-A, relating to conspiracy to wage war against the government. Additionally, he has been booked under the pertinent sections of the Information Technology (IT) Act.
ATS officials stated that their investigation uncovered Maheshwari’s involvement in the conspiracy, motivated by a desire to expedite visa processes for himself, his wife, and two other family members intending to visit Pakistan to meet relatives.
Providing further insights into the case, Jat explained, “Recently, Indian Military Intelligence discovered that either the Pakistan Army or Pakistan’s intelligence agency had gained access to an Indian SIM card. This SIM card was being utilised to spy on Indian defence personnel by delivering malware through WhatsApp. Acting on this intelligence, we arrested Maheshwari in Tarapur, Anand, where he operates a grocery shop.”
The ATS asserts that Maheshwari facilitated Pakistani agents in obtaining an Indian SIM card, which was subsequently employed to breach the security of mobile phones used by the wards of Indian defense personnel attending Army schools.
According to the ATS investigation, the SIM card was issued in the name of Muhammad Saklain Thaim from Jamnagar. It was later activated on the mobile device registered under Azgar Hajibhai’s name. Following activation, the SIM card was delivered to Labhshankar Maheshwari in Tarapur, Anand, upon the instructions of an individual affiliated with the Pakistan Embassy.
Following instructions, Maheshwari, disguising himself as an employee of an Army school, initiated communication with defence personnel. He would prompt them to download an ‘apk’ file and submit their children’s information on the official school website, explained the ATS official.
Jat elaborated, “In reality, that ‘apk’ file was a Remote Access Trojan, a type of malware that extracts all the information from a mobile phone, such as contacts, location, and videos, and sends the data to a command and control centre outside India. As of now, we found that the mobile phone of a soldier stationed at Kargil was compromised with that malware. We are yet to ascertain how many more persons were targeted.”
Sources familiar with the matter disclosed that in 2022, Maheshwari visited his parents in Pakistan. It is believed that Pakistani agents established a connection with him during the processing of his Pakistani visa. Throughout his six-week visit, he is suspected to have been in contact with a Pakistani intelligence agency, sources claimed.
The investigation revealed that at one juncture, Maheshwari assumed the role of an army school employee and convinced parents to download a file, falsely claiming it was necessary for recording specific information.
Furthermore, he deceitfully linked the apk file to the government’s ‘Har Ghar Tiranga’ campaign. Exploiting this false premise, he persuaded numerous army personnel to install the application. In addition to urging recipients to install the app, he would request them to upload a photo of their child with the national flag. However, it is alleged that the trojan malware was actually collecting sensitive information.
While the investigation continues, officials have indicated that other suspects in the case are currently evading capture and are believed to have left the country.