In the world of rising cyber threats, Arishti Info Labs helps organisations with large-scale operational technology by mitigating any security threat to the system. It works to secure Industrial Internet of Things (IIoT),
ICS and other system networks in the OT environment of manufacturing, water, oil & gas, power, chemical, automotive, transport, pharmaceutical and healthcare.
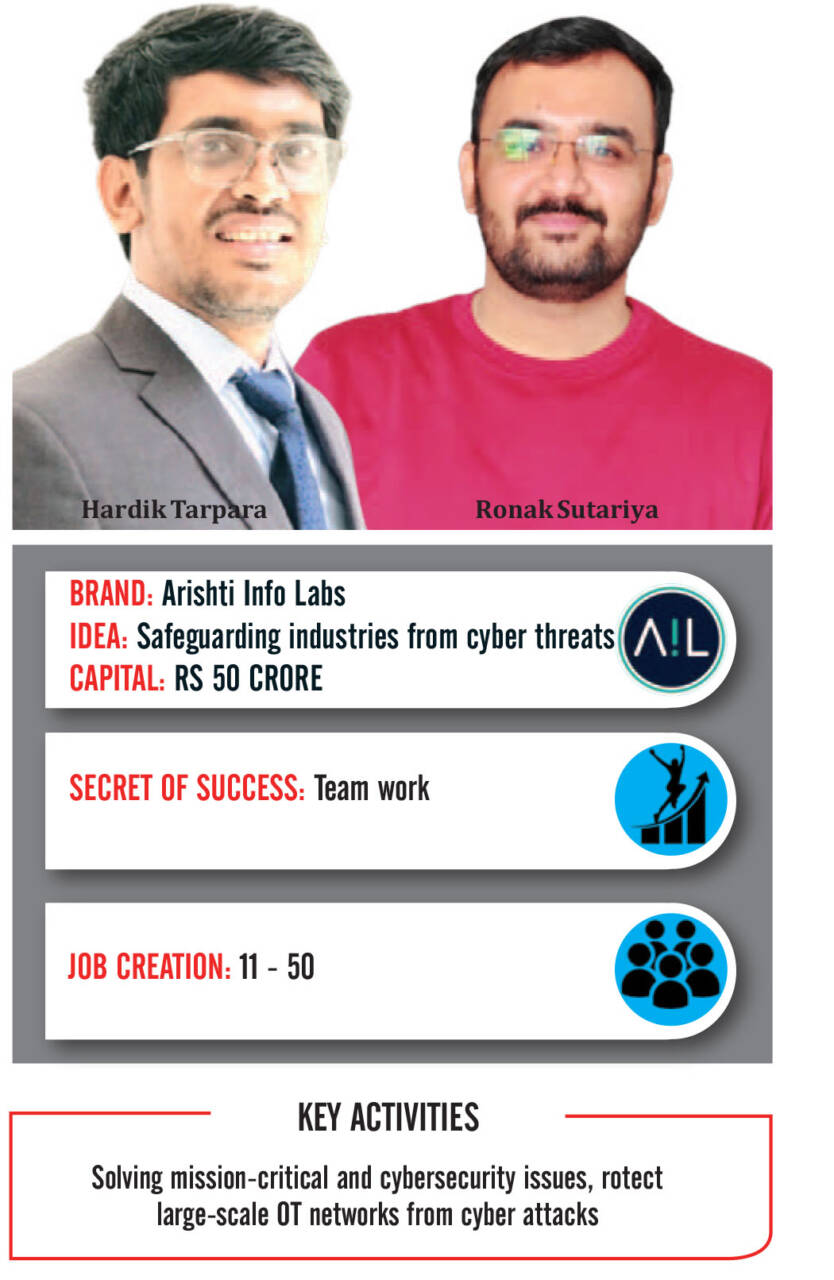
Arishti Info Labs works to safeguard the industries from cyber security threats and risks. Interestingly, Arishti is an adaptation of Sanskrit word that means security or safety. It has employed a team of certified experts on Industrial Control System (ICS), Supervisory Control and Data Acquisition (SCADA), and Operational Technology (OT).
Arishti works in a manner to instill trust in industrial society by solving mission-critical and cybersecurity issues. It has the most trusted ICS and SCADA security partners who work to ensure operational data integrity.
It is well equipped with knowledge, skills, and technological advancements to provide cybersecurity solutions for organisations with complex IIoT/ICS infrastructure.
Our Mission
While working through different jobs, founders Ronak Sutariya and Hardik Tarpara found that industrial operational technology networks are not geared for defending cyber threats due to the shortcomings in system design. Thus, Arishti Info Labs was set up with a mission to eliminate cyber threats for IIoT/ICS/SCADA in the industrial OT environment.
Keeping Hackers At Bay
Due to lack of resources and proper security control measures, industrial control systems have become an easy target for hackers. Also, measures to secure such systems and information are not enough. Thus, Arishti Info Labs works efficiently to protect large-scale OT networks from cyber attacks.
Initial phase
In 2018, the founders were classmates at the National Forensic Sciences University, specialising in Cyber Security and Incident Response. During their capstone project, the duo identified the shortcomings in the ability of industrial OT/SCADA to counteract cyber threats. While engaged in their capstone projects, founders Hardik Tarpara and Ronak Sutariya recognised the vulnerability of industrial operational technology networks to cyber threats due to inherent system design deficiencies. As a result, Arishti Info Labs was established with the mission to eliminate cyber threats within the IIoT/ICS/SCADA industrial OT environment.
Challenges
On this path of becoming a founder, Arishti Info Labs faced hurdles on every single step. It learned that the journey of a founder is always different due to differences in domain, knowledge, culture and values. Therefore, Arishti Info Lab is inspired by solutions incorporated by other founders. The most important part that it has learned as a founder is that the faith of employees actually stirs the company and the sales of the product actually boosts the company.
Market Size
Bharat alone has more than 18,000 companies with annual revenue of more than 10 crores. Arishti Info Lab can easily market its products to these companies. Further, there are more than 5000 industries with annual revenue greater than 25 crores. These would be our main target customers. Two per cent budget awarded to cybersecurity would make this Rs 4, 000 crores industry in Bharat alone.
Founders’ Background
Hardik Tarpara
With more than six years of experience in IoT Development and Security, Hardik is among few security experts who are capable of securing M-2-M architecture. Hardik is responsible for sales and marketing of products and services. He is currently pursuing PhD. from National Forensic Science University and has exceptional knowledge in Cyber Security and Incidences Response.
Ronak Sutariya
As co-founder of Arishti Info Labs, Ronak has knowledge in securing IT and OT environment. He has experience in security consulting and researching working with various industries to help strengthen their industrial infrastructure.
Future Vision
While laying the foundation stone, Arishti Info Labs had a vision of becoming a leader in defending OT networks in ICS and SCADA setup. And for that, Arishti had employed ICS, SCADA, and OT practitioners who have proficiency to find vulnerability in the system through extensive audits and defend the system before cyber incidence. Its work reflects its dedication and core values it espouses as a team and individuals. Its values help it in its journey to become a leader by addressing the cybersecurity threat.




















Comments